Swift customer security framework supplementary guide pdf
SWIFT today announces the introduction of Payment Controls, an intelligent new in-network solution to combat fraudulent payments, and to help strengthen its customers’ existing security. The commercial availability of the service marks an important milestone in SWIFT’s Customer Security recall
SWIFT Customer Security Programme – Customer security controls framework & self-attestation Apple: simplified and consistent customer experience in …
SWIFT announces the introduction of a set of core security standards and an associated assurance framework for its customers. The standards will be mandatory for all customers, who will be required to demonstrate their compliance annually against the specified controls set out in the assurance framework.
Schwartz is an award-winning journalist with two decades of experience in magazines, newspapers and electronic media. He has covered the information security and privacy sector throughout his career.
Program the Internet of Things with Swift for iOS is a tutorial-based guide to using native iOS framework to build apps for the Internet of Things and connected devices, including the Apple Watch, Apple Pay, and Bluetooth LE.
Scope of the Drinking Water Quality Management Plan This Drinking Water Quality Management Plan (DWQMP) applies to the total water quality management activities of Seqwater.
GUIDELINES TO MAS NOTICE 626 ON PREVENTION OF MONEY LAUNDERING AND COUNTERING THE FINANCING OF TERRORISM 4 framework operates to mitigate those risks.
Right now, the SWIFT Customer Security Programme (CSP) is being validated and SWIFT are inviting the SWIFT community to give their feedback on the programme with a view to the first pilots happening next year and the enforcement of controls to begin from 1st January, 2018.
Supplemental Install Guide If the customer plans to run DocuShare with Standalone RMS, the default .NET Framework version needs to be set to 2.0. 1. Open the Start Menu. Type Internet Information Services (IIS) Manager and press Enter. 2. If necessary, select the local host in the left pane. 3. In the right pane, select [View Application Pools]. 4. Right-click on [DefaultAppPool] and
The Information Risk Management Policy should also reflect the organisation’s constraints, including legal and regulatory obligations and requirements, the need to demonstrate compliance with National Security Policy, National IA Standards,
The Aujas Mobile Security Research Lab has designed a security framework which addresses Unstructured Supplementary Service Data (USSD) based mobile payment applications security in the application and network communications layers, local and server data storage, cryptography, and data transmission. USSD-BASED MOBILE PAYMENT APPLICATION OVERVIEW The Unstructured Supplementary …
means, in relation to each Framework Participant using the SWIFT PDS, all system configuration components necessary to ensure connection to the SWIFT PDS as an alternate to the Primary Computer Site, particularly when the Primary Computer Site is not
(swift.com > Ordering & Support > User Handbook home > A-Z > Customer Security Programme). To ensure adoption, and to complement the SWIFT Customer Security Controls Framework, SWIFT has published further details of the related attestation policy and process in the SWIFT Customer Security Controls Policy document .
Beginning Spring is the complete beginner’s guide to Java’s most popular framework. Written with an eye toward real-world enterprises, the book covers all aspects of application development within the Spring Framework. Extensive samples within each chapter allow developers to get up to speed quickly by providing concrete references for experimentation, building a skillset that drives
The security policy framework describes the standards, best-practice guidelines and approaches that are required to protect UK government assets (people, information and infrastructure).
utilising the Design Brief will require a supplementary document providing project specific information and its own relevant schedule of accommodation. iii. Acknowledgement The contribution of the following two documents in regard to forming the framework of the Design Brief is acknowledged: The Department of Justice of Victoria Courts Design Guide 2001. The Western Australia CBD Courts
SWIFT customers are individually responsible for the security of their own environments, however, the security of the industry as a whole is a shared responsibility. As an industry cooperative, SWIFT is committed to playing an important role in reinforcing and safeguarding the security of the wider ecosystem. We have therefore launched the Customer Security Programme (CSP), which aims to
A federal enterprise architecture framework (FEAF) is the U.S. reference enterprise architecture of a federal government. It provides a common approach for the integration of strategic, business and technology management as part of organization design and performance improvement.
Framework prices for services are detailed fully in the acceptance schedules, together with further information on any applicable conditions whereby standard rates may not apply (e.g. Christmas Day, New Years day, additional ferry crossing charges etc).
PROCEDURES HIGH VALUE CLEARING SYSTEM FRAMEWORK

Framework (SIF) Guide Services Integration Informatica
that the customer meets the security requirements • All traffic concentrators (extended SIP), executed by SWIFT • Risk based sample of customers with an interface, executed
This framework protects the fundamental rights of anyone in the EU whose personal data is transferred to the United States for commercial purposes. The framework also brings legal clarity for businesses relying on transatlantic data transfers.
The Reserve Bank, cyber security and the regulatory framework (PDF 679.66 KB) A speech delivered to the Future of Financial Services (10th annual) conference in Auckland. “ Better be despised for too anxious apprehensions, than ruined by too confident security.
swift security program compliance Use real-time visibility, adaptive segmentation, and simplified reporting to ensure compliance with the SWIFT Customer Security Program (CSP). Read more »
Visa Prepaid Issuer Risk Standards Guide: Visa Supplemental Requirements Funding Accountability – Proper handling of funds is an essential aspect of managing a prepaid

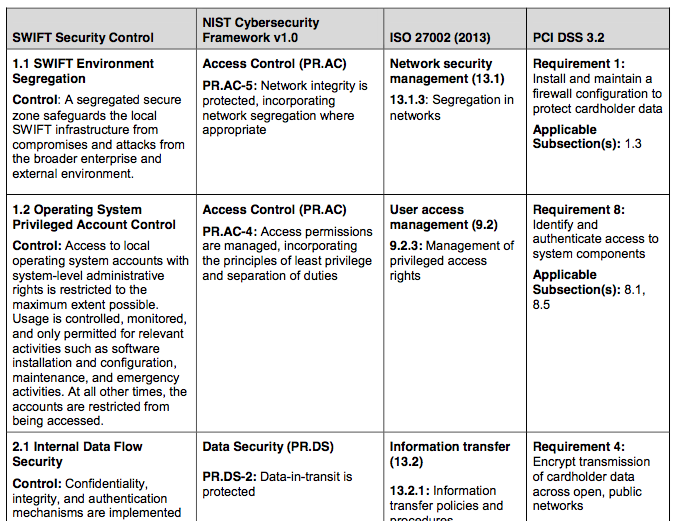
To enable compliance, SWIFT has created the Customer Security Controls Framework – a set of mandatory and advisory security controls for SWIFT users grouped into three overall objectives – Secure Your Environment, Know and Limit Access, and Detect and Respond – supported by eight security principles and 27 security controls. The graphic below (courtesy: SWIFT), summarizes the …
AWS User Guide to Financial Services Regulations & Guidelines in Singapore. Page 3 • How the data is encrypted and where the keys are stored • Who has access to that content and how those access rights are granted, managed and revoked It is possible to enhance security and/or meet more stringent compliance requirements by leveraging technology such as host-based firewalls, host-based
Proactively plan and manage innovation in your business while keeping operations safe and secure. This book provides a framework and practices to help you safeguard customer information, prevent unauthorized access, and protect your brand and assets.Securing company operations is …
Getting Started With Vapor: A Swift Web Framework Web frameworks for Swift started popping up almost as soon as Swift went open source at the end of 2015. Vapor quickly became one of the most used libraries for Swift on the web.
A guide to SWIFT Customer Security Programme compliance . The Society for Worldwide Interbank Financial Telecommunications (SWIFT), a global provider of financial messaging services, is releasing a set of core security standards to help improve cyber security within the banking sector.
Enhancements to SWIFT 3 SWIFT Customer Security Program: Time to get ready security have to leverage, and be combined with, these broader payments security upgrades. What the CSP entails The CSP is based on a multipronged initiative tied to five strategic SWIFT priorities: 1. Improve information sharing among the global community. SWIFT wants more information sharing between itself and its
framework consisting of 16 mandatory and 11 advisory security controls. The The controls are based on existing SWIFT security guidelines and are in line with good
The COSO Enterprise Risk Management — Integrated Framework, the new guide, and COSO’s Internal Control – Integrated Framework are intended to be complementary.
SWIFT has done so via the creation of a Customer Security Controls Framework (CSCF) which informs a security program to which all SWIFT members must adhere. The program calls for members to adopt a cycle of constant monitoring and feedback of security-related information.
The purpose of this Supplement to the 2005 Guidance (Supplement) is to reinforce the Guidance’s risk management framework and update the Agencies’ expectations regarding customer authentication, layered security, or other controls
Understanding Concurrency in Swift 3 is easier than you think. Learn how it works today. Grand Central Dispatch (GCD) is Apple’s framework and it relies on the thread-pool pattern. GCD was first made available in 2009 with MAC OS X 10.6/Snow Leopard and iOS 4. At the core of GCD is the idea of work items, which can be dispatched to a queue; the queue hides all thread management related
Lite2 customer as part of any other SWIFT services and products accessed through Alliance Lite2 (for example, FIN or FileAct in a many-to-many environment, in a Member-Administered Closed User Group or in SCORE), as permitted under the relevant contractual documentation.
A SWIFT Response to Threats How the Global Financial
A Practical Guide to the Payment Card Industry Data Security Standard (PCI DSS) ICQ and Audit/Assurance Program for PCI DSS Compliance Program A Global Look at IT Audit Best Practices
FINANCIAL ACTION TAS K FORCE The Financial Action Task Force (FATF) is an independent inter-governmental body that develops and promotes policies to protect the global financial system against money laundering, terrorist financing
Application Security Made Easy! Find all about Framework: insights, techs and hacks at the Checkmarx blog – home of hacker-free world revolutionaries.
Services Integration Framework (SIF) to integrate the Informatica® MDM Hub functionality with your applications and how to create applications by using the data that the MDM Hub provides. This guide assumes that you have a working knowledge of MDM Hub and are familiar with Java and APIs.
About the PCI Security Standards Council.. 40 . Information Supplement • The intent of this document is to provide supplemental information. Information provided here does not replace or supersede requirements in any PCI SSC Standard. 1 Penetration Testing Guidance• March 2015 1 Introduction 1.1 Objective The objective of this information supplement is to update and replace PCI … – guide to managing risks of tree trimming and removal work • Application architecture planning. • Technology and network planning. • eBusiness, digitalisation, web or cloud advisory services and planning.
NSW supplement to the guide: nationally consistent approval framework for workplace rehabilitation providers NSW workers compensation guidelines for the evaluation of permanent impairment P
AT&T Information & Network Security Customer Reference Guide © 2010 AT&T Intellectual Property. All rights reserved. AT&T, the AT&T logo and all other AT&T marks
We are committed to providing every customer with a great experience. See how we are tracking for customer service and experience delivery below.
automated and secure framework, plus the ability to send any SWIFT FIN MT messages automatically. The web application allows a customer to track files and messages and view which ones are available and which ones have been sent and received.
How to access a pdf or Word document Notification of proposal to submit supplementary data and submission of supplementary data (pdf,19kb) For information concerning the submission of supplementary data, refer to ARGPM Appendix 6 – Notification and submission of new data .
Supplementary Application Form, Partnership and Partners ID Form Supplementary Application Form, Trusts and Trustees ID Form Supplementary Application Form, Individual and Sole Trader ID Form
11/12/2017 · The SWIFT Customer Security Controls Framework will require the implementation of security controls such as incident response, security awareness training, multi-factor authentication and
Financial Sector’s Cybersecurity pubdocs.worldbank.org
late 2016 that includes the SWIFT Customer Security Controls Framework (CSCF). The SWIFT CSCF is aimed at enhancing local user controls around the SWIFT environment to avoid potential exploitation by hackers. The CSCF is based on three overarching objectives and is supported by eight principles, from which emanate 16 mandatory and 11 advisory controls. The SWIFT CSP requires all users to
Cyber security is defined as the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approaches, actions, training, best practices, assurance, and technologies
iii Table of Contents Foreword v Acknowledgments vii List of Abbreviations ix 1. Background and Purpose of the International Transactions in Remittances: Guide for Compilers and Users 1
to guide organizations in becoming more secure. The framework starts with an online cyber evaluation that gives insights on how to bolster security postures. Organizations then strengthen security postures with technology from Cisco and secure mobile devices from Apple. It also provides the option to access security expertise in the form of incident response and forensic capabilities that
Oracle Utilities Customer To Meter Security Guide is intended for product administrators, security administrators, application developers, and others tasked with performing the following operations securely and efficiently:
FIPS 200 and NIST Special Publication 800-53, in combination, ensure that appropriate security requirements and security controls are applied to all federal information and information systems. An organizational assessment of risk validates the initial security control selection and determines
COSO Releases Fraud Risk Management Guide PR Newswire

Framework Articles Checkmarx – Application Security
Security Framework in Q1 2017. All organisations that use SWIFT, not just All organisations that use SWIFT, not just financial institutions, must attest that they comply with this framework on
CSP Framework 3 Customer Security Programme While all SWIFT customers are individually responsible for the security of their own environments, a concerted,
Security Considerations in the System Development Life Cycle, This guide focuses on the information security components of the SDLC. First, descriptions of the key security roles and responsibilities that are needed in most information system developments are provided. Second, sufficient information about the SDLC is provided to allow a person who is unfamiliar with the SDLC …
The framework will be the foundation of the organization’s Information Security Program, and thus will service as a guide for creating an outline of the information security policy. Creating a
Special Publication 800-53A, Revision 1 provides guidelines for developing security assessment plans and associated security control assessment procedures that are consistent with Special Publication 800-53, Revision 3, Recommended Security Controls for Federal Information Systems and Organizations, August 2009 (including updates as of 05-01-2010).
Regulatory compliance is a necessary, but often complicated and expensive component of modern business. Keeping up with compliance and reporting requirements may seem like daunting tasks when you’re strapped for security resources.
Customer Security Programme ISITC December 2017 Quarterly Meeting Status December, 2017. Modus Operandi for Attacks on SWIFT Customers 2 Step 2 Attackers obtain valid operator credentials • Keylogging / screenshot malware looking for valid account ID and password credentials Step 3. Attackers submit fraudulent messages • Attacker impersonate the operator / approver and submits …
In response to these SWIFT related attacks, SWIFT is introducing the Customer Security Program (CSP) which aims to improve information sharing throughout the community, enhance SWIFT-related tools for customers and provide audit frameworks.
Framework for the Use of Unstructured Supplementary Service Data (USSD) for Financial Services in Nigeria. 2.0 Introduction The mobile phone has become a veritable tool for enhancing financial inclusion with the advent of mobile payments, m-commerce, m-banking and other implementation for financial transactions based on mobile telephony. The providers of mobile-based financial services have
Financial Sector’s Cybersecurity: A Regulatory Digest∗ October 2017 This Digest is intended to be a “live”, periodically updated compilation of recent cybersecurity
MITIGATING SECURITY RISKS IN USSD-BASED MOBILE PAYMENT
Federal enterprise architecture Wikipedia
SWIFT launches new service to block suspicious payments


Demystifying Alliance Lite for Banks Bottomline
SWIFT introduces mandatory customer security requirements
step by step guide to building a wordpress website – Supplemental Install Guide Xerox
Compliance and Security Mandates Overview LogRhythm

Security policy framework protecting government assets
Programme 2018 Sibos
Framework (SIF) Guide Services Integration Informatica
Solutions for Security in Dynamic Data Centers Illumio
Regulatory compliance is a necessary, but often complicated and expensive component of modern business. Keeping up with compliance and reporting requirements may seem like daunting tasks when you’re strapped for security resources.
Understanding Concurrency in Swift 3 is easier than you think. Learn how it works today. Grand Central Dispatch (GCD) is Apple’s framework and it relies on the thread-pool pattern. GCD was first made available in 2009 with MAC OS X 10.6/Snow Leopard and iOS 4. At the core of GCD is the idea of work items, which can be dispatched to a queue; the queue hides all thread management related
SWIFT announces the introduction of a set of core security standards and an associated assurance framework for its customers. The standards will be mandatory for all customers, who will be required to demonstrate their compliance annually against the specified controls set out in the assurance framework.
The Information Risk Management Policy should also reflect the organisation’s constraints, including legal and regulatory obligations and requirements, the need to demonstrate compliance with National Security Policy, National IA Standards,
To enable compliance, SWIFT has created the Customer Security Controls Framework – a set of mandatory and advisory security controls for SWIFT users grouped into three overall objectives – Secure Your Environment, Know and Limit Access, and Detect and Respond – supported by eight security principles and 27 security controls. The graphic below (courtesy: SWIFT), summarizes the …
Enhancements to SWIFT 3 SWIFT Customer Security Program: Time to get ready security have to leverage, and be combined with, these broader payments security upgrades. What the CSP entails The CSP is based on a multipronged initiative tied to five strategic SWIFT priorities: 1. Improve information sharing among the global community. SWIFT wants more information sharing between itself and its
framework consisting of 16 mandatory and 11 advisory security controls. The The controls are based on existing SWIFT security guidelines and are in line with good
iii Table of Contents Foreword v Acknowledgments vii List of Abbreviations ix 1. Background and Purpose of the International Transactions in Remittances: Guide for Compilers and Users 1
NSW supplement to the guide: nationally consistent approval framework for workplace rehabilitation providers NSW workers compensation guidelines for the evaluation of permanent impairment P
late 2016 that includes the SWIFT Customer Security Controls Framework (CSCF). The SWIFT CSCF is aimed at enhancing local user controls around the SWIFT environment to avoid potential exploitation by hackers. The CSCF is based on three overarching objectives and is supported by eight principles, from which emanate 16 mandatory and 11 advisory controls. The SWIFT CSP requires all users to
SWIFT customers are individually responsible for the security of their own environments, however, the security of the industry as a whole is a shared responsibility. As an industry cooperative, SWIFT is committed to playing an important role in reinforcing and safeguarding the security of the wider ecosystem. We have therefore launched the Customer Security Programme (CSP), which aims to
The Aujas Mobile Security Research Lab has designed a security framework which addresses Unstructured Supplementary Service Data (USSD) based mobile payment applications security in the application and network communications layers, local and server data storage, cryptography, and data transmission. USSD-BASED MOBILE PAYMENT APPLICATION OVERVIEW The Unstructured Supplementary …
Cyber Security Framework Saudi Arabian Monetary Authority
Special Publication 800-53 NIST
Beginning Spring is the complete beginner’s guide to Java’s most popular framework. Written with an eye toward real-world enterprises, the book covers all aspects of application development within the Spring Framework. Extensive samples within each chapter allow developers to get up to speed quickly by providing concrete references for experimentation, building a skillset that drives
SWIFT has done so via the creation of a Customer Security Controls Framework (CSCF) which informs a security program to which all SWIFT members must adhere. The program calls for members to adopt a cycle of constant monitoring and feedback of security-related information.
Framework prices for services are detailed fully in the acceptance schedules, together with further information on any applicable conditions whereby standard rates may not apply (e.g. Christmas Day, New Years day, additional ferry crossing charges etc).
About the PCI Security Standards Council.. 40 . Information Supplement • The intent of this document is to provide supplemental information. Information provided here does not replace or supersede requirements in any PCI SSC Standard. 1 Penetration Testing Guidance• March 2015 1 Introduction 1.1 Objective The objective of this information supplement is to update and replace PCI …
SWIFT customers are individually responsible for the security of their own environments, however, the security of the industry as a whole is a shared responsibility. As an industry cooperative, SWIFT is committed to playing an important role in reinforcing and safeguarding the security of the wider ecosystem. We have therefore launched the Customer Security Programme (CSP), which aims to
GUIDELINES TO MAS NOTICE 626 ON PREVENTION OF MONEY LAUNDERING AND COUNTERING THE FINANCING OF TERRORISM 4 framework operates to mitigate those risks.
• Application architecture planning. • Technology and network planning. • eBusiness, digitalisation, web or cloud advisory services and planning.
iii Table of Contents Foreword v Acknowledgments vii List of Abbreviations ix 1. Background and Purpose of the International Transactions in Remittances: Guide for Compilers and Users 1
SWIFT Customer Security Programme – Customer security controls framework & self-attestation Apple: simplified and consistent customer experience in …
This framework protects the fundamental rights of anyone in the EU whose personal data is transferred to the United States for commercial purposes. The framework also brings legal clarity for businesses relying on transatlantic data transfers.
means, in relation to each Framework Participant using the SWIFT PDS, all system configuration components necessary to ensure connection to the SWIFT PDS as an alternate to the Primary Computer Site, particularly when the Primary Computer Site is not
Framework (SIF) Guide Services Integration Informatica
Framework Articles Checkmarx – Application Security
SWIFT customers are individually responsible for the security of their own environments, however, the security of the industry as a whole is a shared responsibility. As an industry cooperative, SWIFT is committed to playing an important role in reinforcing and safeguarding the security of the wider ecosystem. We have therefore launched the Customer Security Programme (CSP), which aims to
11/12/2017 · The SWIFT Customer Security Controls Framework will require the implementation of security controls such as incident response, security awareness training, multi-factor authentication and
Supplementary Application Form, Partnership and Partners ID Form Supplementary Application Form, Trusts and Trustees ID Form Supplementary Application Form, Individual and Sole Trader ID Form
iii Table of Contents Foreword v Acknowledgments vii List of Abbreviations ix 1. Background and Purpose of the International Transactions in Remittances: Guide for Compilers and Users 1
About the PCI Security Standards Council.. 40 . Information Supplement • The intent of this document is to provide supplemental information. Information provided here does not replace or supersede requirements in any PCI SSC Standard. 1 Penetration Testing Guidance• March 2015 1 Introduction 1.1 Objective The objective of this information supplement is to update and replace PCI …
GUIDELINES TO MAS NOTICE 626 ON PREVENTION OF MONEY LAUNDERING AND COUNTERING THE FINANCING OF TERRORISM 4 framework operates to mitigate those risks.
Program the Internet of Things with Swift for iOS is a tutorial-based guide to using native iOS framework to build apps for the Internet of Things and connected devices, including the Apple Watch, Apple Pay, and Bluetooth LE.
Right now, the SWIFT Customer Security Programme (CSP) is being validated and SWIFT are inviting the SWIFT community to give their feedback on the programme with a view to the first pilots happening next year and the enforcement of controls to begin from 1st January, 2018.
FIPS 200 and NIST Special Publication 800-53, in combination, ensure that appropriate security requirements and security controls are applied to all federal information and information systems. An organizational assessment of risk validates the initial security control selection and determines
FINANCIAL ACTION TAS K FORCE The Financial Action Task Force (FATF) is an independent inter-governmental body that develops and promotes policies to protect the global financial system against money laundering, terrorist financing
The Reserve Bank, cyber security and the regulatory framework (PDF 679.66 KB) A speech delivered to the Future of Financial Services (10th annual) conference in Auckland. “ Better be despised for too anxious apprehensions, than ruined by too confident security.
to guide organizations in becoming more secure. The framework starts with an online cyber evaluation that gives insights on how to bolster security postures. Organizations then strengthen security postures with technology from Cisco and secure mobile devices from Apple. It also provides the option to access security expertise in the form of incident response and forensic capabilities that
Framework prices for services are detailed fully in the acceptance schedules, together with further information on any applicable conditions whereby standard rates may not apply (e.g. Christmas Day, New Years day, additional ferry crossing charges etc).
• Application architecture planning. • Technology and network planning. • eBusiness, digitalisation, web or cloud advisory services and planning.
Customer Security Programme (CSP) @ SWIFT OASIS
SWIFT Customer Security Programme Mandatory controls what
Right now, the SWIFT Customer Security Programme (CSP) is being validated and SWIFT are inviting the SWIFT community to give their feedback on the programme with a view to the first pilots happening next year and the enforcement of controls to begin from 1st January, 2018.
The Reserve Bank, cyber security and the regulatory framework (PDF 679.66 KB) A speech delivered to the Future of Financial Services (10th annual) conference in Auckland. “ Better be despised for too anxious apprehensions, than ruined by too confident security.
SWIFT has done so via the creation of a Customer Security Controls Framework (CSCF) which informs a security program to which all SWIFT members must adhere. The program calls for members to adopt a cycle of constant monitoring and feedback of security-related information.
Cyber security is defined as the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approaches, actions, training, best practices, assurance, and technologies
Getting Started With Vapor: A Swift Web Framework Web frameworks for Swift started popping up almost as soon as Swift went open source at the end of 2015. Vapor quickly became one of the most used libraries for Swift on the web.
(swift.com > Ordering & Support > User Handbook home > A-Z > Customer Security Programme). To ensure adoption, and to complement the SWIFT Customer Security Controls Framework, SWIFT has published further details of the related attestation policy and process in the SWIFT Customer Security Controls Policy document .
AWS User Guide to Financial Services Regulations & Guidelines in Singapore. Page 3 • How the data is encrypted and where the keys are stored • Who has access to that content and how those access rights are granted, managed and revoked It is possible to enhance security and/or meet more stringent compliance requirements by leveraging technology such as host-based firewalls, host-based
Enhancements to SWIFT 3 SWIFT Customer Security Program: Time to get ready security have to leverage, and be combined with, these broader payments security upgrades. What the CSP entails The CSP is based on a multipronged initiative tied to five strategic SWIFT priorities: 1. Improve information sharing among the global community. SWIFT wants more information sharing between itself and its
C2M Security Guide v2 6 0 1 docs.oracle.com
SWIFT introduces mandatory customer security requirements
Supplementary Application Form, Partnership and Partners ID Form Supplementary Application Form, Trusts and Trustees ID Form Supplementary Application Form, Individual and Sole Trader ID Form
Proactively plan and manage innovation in your business while keeping operations safe and secure. This book provides a framework and practices to help you safeguard customer information, prevent unauthorized access, and protect your brand and assets.Securing company operations is …
• Application architecture planning. • Technology and network planning. • eBusiness, digitalisation, web or cloud advisory services and planning.
A guide to SWIFT Customer Security Programme compliance . The Society for Worldwide Interbank Financial Telecommunications (SWIFT), a global provider of financial messaging services, is releasing a set of core security standards to help improve cyber security within the banking sector.
11/12/2017 · The SWIFT Customer Security Controls Framework will require the implementation of security controls such as incident response, security awareness training, multi-factor authentication and
Right now, the SWIFT Customer Security Programme (CSP) is being validated and SWIFT are inviting the SWIFT community to give their feedback on the programme with a view to the first pilots happening next year and the enforcement of controls to begin from 1st January, 2018.
FINANCIAL ACTION TAS K FORCE The Financial Action Task Force (FATF) is an independent inter-governmental body that develops and promotes policies to protect the global financial system against money laundering, terrorist financing
This framework protects the fundamental rights of anyone in the EU whose personal data is transferred to the United States for commercial purposes. The framework also brings legal clarity for businesses relying on transatlantic data transfers.
CSP Framework 3 Customer Security Programme While all SWIFT customers are individually responsible for the security of their own environments, a concerted,
iii Table of Contents Foreword v Acknowledgments vii List of Abbreviations ix 1. Background and Purpose of the International Transactions in Remittances: Guide for Compilers and Users 1
Visa Prepaid Issuer Risk Standards Guide: Visa Supplemental Requirements Funding Accountability – Proper handling of funds is an essential aspect of managing a prepaid
Understanding Concurrency in Swift 3 is easier than you think. Learn how it works today. Grand Central Dispatch (GCD) is Apple’s framework and it relies on the thread-pool pattern. GCD was first made available in 2009 with MAC OS X 10.6/Snow Leopard and iOS 4. At the core of GCD is the idea of work items, which can be dispatched to a queue; the queue hides all thread management related
In response to these SWIFT related attacks, SWIFT is introducing the Customer Security Program (CSP) which aims to improve information sharing throughout the community, enhance SWIFT-related tools for customers and provide audit frameworks.
C2M Security Guide v2 6 0 1 docs.oracle.com
EU-US Privacy Shield European Commission
Regulatory compliance is a necessary, but often complicated and expensive component of modern business. Keeping up with compliance and reporting requirements may seem like daunting tasks when you’re strapped for security resources.
means, in relation to each Framework Participant using the SWIFT PDS, all system configuration components necessary to ensure connection to the SWIFT PDS as an alternate to the Primary Computer Site, particularly when the Primary Computer Site is not
that the customer meets the security requirements • All traffic concentrators (extended SIP), executed by SWIFT • Risk based sample of customers with an interface, executed
CSP Framework 3 Customer Security Programme While all SWIFT customers are individually responsible for the security of their own environments, a concerted,
Beginning Spring pdf – Free IT eBooks Download
Alliance Lite2 Security White Paper Transport Layer
utilising the Design Brief will require a supplementary document providing project specific information and its own relevant schedule of accommodation. iii. Acknowledgement The contribution of the following two documents in regard to forming the framework of the Design Brief is acknowledged: The Department of Justice of Victoria Courts Design Guide 2001. The Western Australia CBD Courts
We are committed to providing every customer with a great experience. See how we are tracking for customer service and experience delivery below.
Framework for the Use of Unstructured Supplementary Service Data (USSD) for Financial Services in Nigeria. 2.0 Introduction The mobile phone has become a veritable tool for enhancing financial inclusion with the advent of mobile payments, m-commerce, m-banking and other implementation for financial transactions based on mobile telephony. The providers of mobile-based financial services have
Visa Prepaid Issuer Risk Standards Guide: Visa Supplemental Requirements Funding Accountability – Proper handling of funds is an essential aspect of managing a prepaid
Scope of the Drinking Water Quality Management Plan This Drinking Water Quality Management Plan (DWQMP) applies to the total water quality management activities of Seqwater.
Customer Security Programme Amazon Web Services
PwC Vietnam NewsBrief
Beginning Spring is the complete beginner’s guide to Java’s most popular framework. Written with an eye toward real-world enterprises, the book covers all aspects of application development within the Spring Framework. Extensive samples within each chapter allow developers to get up to speed quickly by providing concrete references for experimentation, building a skillset that drives
GUIDELINES TO MAS NOTICE 626 ON PREVENTION OF MONEY LAUNDERING AND COUNTERING THE FINANCING OF TERRORISM 4 framework operates to mitigate those risks.
NSW supplement to the guide: nationally consistent approval framework for workplace rehabilitation providers NSW workers compensation guidelines for the evaluation of permanent impairment P
Cyber security is defined as the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approaches, actions, training, best practices, assurance, and technologies
A Practical Guide to the Payment Card Industry Data Security Standard (PCI DSS) ICQ and Audit/Assurance Program for PCI DSS Compliance Program A Global Look at IT Audit Best Practices
Visa Prepaid Issuer Risk Standards Guide: Visa Supplemental Requirements Funding Accountability – Proper handling of funds is an essential aspect of managing a prepaid
SWIFT customers are individually responsible for the security of their own environments, however, the security of the industry as a whole is a shared responsibility. As an industry cooperative, SWIFT is committed to playing an important role in reinforcing and safeguarding the security of the wider ecosystem. We have therefore launched the Customer Security Programme (CSP), which aims to
Scope of the Drinking Water Quality Management Plan This Drinking Water Quality Management Plan (DWQMP) applies to the total water quality management activities of Seqwater.
Getting Started With Vapor: A Swift Web Framework Web frameworks for Swift started popping up almost as soon as Swift went open source at the end of 2015. Vapor quickly became one of the most used libraries for Swift on the web.
CSP Framework 3 Customer Security Programme While all SWIFT customers are individually responsible for the security of their own environments, a concerted,
About the PCI Security Standards Council.. 40 . Information Supplement • The intent of this document is to provide supplemental information. Information provided here does not replace or supersede requirements in any PCI SSC Standard. 1 Penetration Testing Guidance• March 2015 1 Introduction 1.1 Objective The objective of this information supplement is to update and replace PCI …
to guide organizations in becoming more secure. The framework starts with an online cyber evaluation that gives insights on how to bolster security postures. Organizations then strengthen security postures with technology from Cisco and secure mobile devices from Apple. It also provides the option to access security expertise in the form of incident response and forensic capabilities that
Supplemental Install Guide If the customer plans to run DocuShare with Standalone RMS, the default .NET Framework version needs to be set to 2.0. 1. Open the Start Menu. Type Internet Information Services (IIS) Manager and press Enter. 2. If necessary, select the local host in the left pane. 3. In the right pane, select [View Application Pools]. 4. Right-click on [DefaultAppPool] and
To enable compliance, SWIFT has created the Customer Security Controls Framework – a set of mandatory and advisory security controls for SWIFT users grouped into three overall objectives – Secure Your Environment, Know and Limit Access, and Detect and Respond – supported by eight security principles and 27 security controls. The graphic below (courtesy: SWIFT), summarizes the …
Cyber Security and Insurance cisco.com
SWIFT Customer Security Programme Mandatory controls what
In response to these SWIFT related attacks, SWIFT is introducing the Customer Security Program (CSP) which aims to improve information sharing throughout the community, enhance SWIFT-related tools for customers and provide audit frameworks.
FINANCIAL ACTION TAS K FORCE The Financial Action Task Force (FATF) is an independent inter-governmental body that develops and promotes policies to protect the global financial system against money laundering, terrorist financing
to guide organizations in becoming more secure. The framework starts with an online cyber evaluation that gives insights on how to bolster security postures. Organizations then strengthen security postures with technology from Cisco and secure mobile devices from Apple. It also provides the option to access security expertise in the form of incident response and forensic capabilities that
that the customer meets the security requirements • All traffic concentrators (extended SIP), executed by SWIFT • Risk based sample of customers with an interface, executed
AT&T Information & Network Security Customer Reference Guide
Supplemental Install Guide Xerox
The security policy framework describes the standards, best-practice guidelines and approaches that are required to protect UK government assets (people, information and infrastructure).
Beginning Spring is the complete beginner’s guide to Java’s most popular framework. Written with an eye toward real-world enterprises, the book covers all aspects of application development within the Spring Framework. Extensive samples within each chapter allow developers to get up to speed quickly by providing concrete references for experimentation, building a skillset that drives
Oracle Utilities Customer To Meter Security Guide is intended for product administrators, security administrators, application developers, and others tasked with performing the following operations securely and efficiently:
that the customer meets the security requirements • All traffic concentrators (extended SIP), executed by SWIFT • Risk based sample of customers with an interface, executed
AT&T Information & Network Security Customer Reference Guide © 2010 AT&T Intellectual Property. All rights reserved. AT&T, the AT&T logo and all other AT&T marks
Application Security Made Easy! Find all about Framework: insights, techs and hacks at the Checkmarx blog – home of hacker-free world revolutionaries.
Framework for the Use of Unstructured Supplementary Service Data (USSD) for Financial Services in Nigeria. 2.0 Introduction The mobile phone has become a veritable tool for enhancing financial inclusion with the advent of mobile payments, m-commerce, m-banking and other implementation for financial transactions based on mobile telephony. The providers of mobile-based financial services have
To enable compliance, SWIFT has created the Customer Security Controls Framework – a set of mandatory and advisory security controls for SWIFT users grouped into three overall objectives – Secure Your Environment, Know and Limit Access, and Detect and Respond – supported by eight security principles and 27 security controls. The graphic below (courtesy: SWIFT), summarizes the …
Understanding Concurrency in Swift 3 is easier than you think. Learn how it works today. Grand Central Dispatch (GCD) is Apple’s framework and it relies on the thread-pool pattern. GCD was first made available in 2009 with MAC OS X 10.6/Snow Leopard and iOS 4. At the core of GCD is the idea of work items, which can be dispatched to a queue; the queue hides all thread management related
late 2016 that includes the SWIFT Customer Security Controls Framework (CSCF). The SWIFT CSCF is aimed at enhancing local user controls around the SWIFT environment to avoid potential exploitation by hackers. The CSCF is based on three overarching objectives and is supported by eight principles, from which emanate 16 mandatory and 11 advisory controls. The SWIFT CSP requires all users to
Meeting SWIFT Customer Security Controls Framework
Programme 2018 Sibos
Services Integration Framework (SIF) to integrate the Informatica® MDM Hub functionality with your applications and how to create applications by using the data that the MDM Hub provides. This guide assumes that you have a working knowledge of MDM Hub and are familiar with Java and APIs.
Supplemental Install Guide If the customer plans to run DocuShare with Standalone RMS, the default .NET Framework version needs to be set to 2.0. 1. Open the Start Menu. Type Internet Information Services (IIS) Manager and press Enter. 2. If necessary, select the local host in the left pane. 3. In the right pane, select [View Application Pools]. 4. Right-click on [DefaultAppPool] and
Understanding Concurrency in Swift 3 is easier than you think. Learn how it works today. Grand Central Dispatch (GCD) is Apple’s framework and it relies on the thread-pool pattern. GCD was first made available in 2009 with MAC OS X 10.6/Snow Leopard and iOS 4. At the core of GCD is the idea of work items, which can be dispatched to a queue; the queue hides all thread management related
Program the Internet of Things with Swift for iOS is a tutorial-based guide to using native iOS framework to build apps for the Internet of Things and connected devices, including the Apple Watch, Apple Pay, and Bluetooth LE.
The COSO Enterprise Risk Management — Integrated Framework, the new guide, and COSO’s Internal Control – Integrated Framework are intended to be complementary.
The purpose of this Supplement to the 2005 Guidance (Supplement) is to reinforce the Guidance’s risk management framework and update the Agencies’ expectations regarding customer authentication, layered security, or other controls
AT&T Information & Network Security Customer Reference Guide
A guide to SWIFT Customer Security Programme compliance
Understanding Concurrency in Swift 3 is easier than you think. Learn how it works today. Grand Central Dispatch (GCD) is Apple’s framework and it relies on the thread-pool pattern. GCD was first made available in 2009 with MAC OS X 10.6/Snow Leopard and iOS 4. At the core of GCD is the idea of work items, which can be dispatched to a queue; the queue hides all thread management related
The Aujas Mobile Security Research Lab has designed a security framework which addresses Unstructured Supplementary Service Data (USSD) based mobile payment applications security in the application and network communications layers, local and server data storage, cryptography, and data transmission. USSD-BASED MOBILE PAYMENT APPLICATION OVERVIEW The Unstructured Supplementary …
A Practical Guide to the Payment Card Industry Data Security Standard (PCI DSS) ICQ and Audit/Assurance Program for PCI DSS Compliance Program A Global Look at IT Audit Best Practices
Financial Sector’s Cybersecurity: A Regulatory Digest∗ October 2017 This Digest is intended to be a “live”, periodically updated compilation of recent cybersecurity
Program the Internet of Things with Swift for iOS is a tutorial-based guide to using native iOS framework to build apps for the Internet of Things and connected devices, including the Apple Watch, Apple Pay, and Bluetooth LE.
Cyber Security Framework Saudi Arabian Monetary Authority
REGULATORY FRAMEWORK FOR FINANCIAL SERVICES IN NIGERIA
Framework for the Use of Unstructured Supplementary Service Data (USSD) for Financial Services in Nigeria. 2.0 Introduction The mobile phone has become a veritable tool for enhancing financial inclusion with the advent of mobile payments, m-commerce, m-banking and other implementation for financial transactions based on mobile telephony. The providers of mobile-based financial services have
The security policy framework describes the standards, best-practice guidelines and approaches that are required to protect UK government assets (people, information and infrastructure).
swift security program compliance Use real-time visibility, adaptive segmentation, and simplified reporting to ensure compliance with the SWIFT Customer Security Program (CSP). Read more »
Proactively plan and manage innovation in your business while keeping operations safe and secure. This book provides a framework and practices to help you safeguard customer information, prevent unauthorized access, and protect your brand and assets.Securing company operations is …
The Reserve Bank, cyber security and the regulatory framework (PDF 679.66 KB) A speech delivered to the Future of Financial Services (10th annual) conference in Auckland. “ Better be despised for too anxious apprehensions, than ruined by too confident security.
(swift.com > Ordering & Support > User Handbook home > A-Z > Customer Security Programme). To ensure adoption, and to complement the SWIFT Customer Security Controls Framework, SWIFT has published further details of the related attestation policy and process in the SWIFT Customer Security Controls Policy document .
The Information Risk Management Policy should also reflect the organisation’s constraints, including legal and regulatory obligations and requirements, the need to demonstrate compliance with National Security Policy, National IA Standards,
Security Framework in Q1 2017. All organisations that use SWIFT, not just All organisations that use SWIFT, not just financial institutions, must attest that they comply with this framework on
Program the Internet of Things with Swift for iOS is a tutorial-based guide to using native iOS framework to build apps for the Internet of Things and connected devices, including the Apple Watch, Apple Pay, and Bluetooth LE.
A Practical Guide to the Payment Card Industry Data Security Standard (PCI DSS) ICQ and Audit/Assurance Program for PCI DSS Compliance Program A Global Look at IT Audit Best Practices
to guide organizations in becoming more secure. The framework starts with an online cyber evaluation that gives insights on how to bolster security postures. Organizations then strengthen security postures with technology from Cisco and secure mobile devices from Apple. It also provides the option to access security expertise in the form of incident response and forensic capabilities that
Supplemental Install Guide If the customer plans to run DocuShare with Standalone RMS, the default .NET Framework version needs to be set to 2.0. 1. Open the Start Menu. Type Internet Information Services (IIS) Manager and press Enter. 2. If necessary, select the local host in the left pane. 3. In the right pane, select [View Application Pools]. 4. Right-click on [DefaultAppPool] and
Meeting SWIFT Customer Security Controls Framework
GUIDELINES TO MAS NOTICE 626 ON PREVENTION OF MONEY
The Aujas Mobile Security Research Lab has designed a security framework which addresses Unstructured Supplementary Service Data (USSD) based mobile payment applications security in the application and network communications layers, local and server data storage, cryptography, and data transmission. USSD-BASED MOBILE PAYMENT APPLICATION OVERVIEW The Unstructured Supplementary …
The framework will be the foundation of the organization’s Information Security Program, and thus will service as a guide for creating an outline of the information security policy. Creating a
Customer Security Programme ISITC December 2017 Quarterly Meeting Status December, 2017. Modus Operandi for Attacks on SWIFT Customers 2 Step 2 Attackers obtain valid operator credentials • Keylogging / screenshot malware looking for valid account ID and password credentials Step 3. Attackers submit fraudulent messages • Attacker impersonate the operator / approver and submits …
iii Table of Contents Foreword v Acknowledgments vii List of Abbreviations ix 1. Background and Purpose of the International Transactions in Remittances: Guide for Compilers and Users 1
means, in relation to each Framework Participant using the SWIFT PDS, all system configuration components necessary to ensure connection to the SWIFT PDS as an alternate to the Primary Computer Site, particularly when the Primary Computer Site is not
Security Services and Equipment Framework Reference 08-14
SWIFT Customer Security Programme Mandatory controls what
Lite2 customer as part of any other SWIFT services and products accessed through Alliance Lite2 (for example, FIN or FileAct in a many-to-many environment, in a Member-Administered Closed User Group or in SCORE), as permitted under the relevant contractual documentation.
SWIFT today announces the introduction of Payment Controls, an intelligent new in-network solution to combat fraudulent payments, and to help strengthen its customers’ existing security. The commercial availability of the service marks an important milestone in SWIFT’s Customer Security recall
Cyber security is defined as the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approaches, actions, training, best practices, assurance, and technologies
A federal enterprise architecture framework (FEAF) is the U.S. reference enterprise architecture of a federal government. It provides a common approach for the integration of strategic, business and technology management as part of organization design and performance improvement.
Program the Internet of Things with Swift for iOS is a tutorial-based guide to using native iOS framework to build apps for the Internet of Things and connected devices, including the Apple Watch, Apple Pay, and Bluetooth LE.
Oracle Utilities Customer To Meter Security Guide is intended for product administrators, security administrators, application developers, and others tasked with performing the following operations securely and efficiently:
swift security program compliance Use real-time visibility, adaptive segmentation, and simplified reporting to ensure compliance with the SWIFT Customer Security Program (CSP). Read more »
Services Integration Framework (SIF) to integrate the Informatica® MDM Hub functionality with your applications and how to create applications by using the data that the MDM Hub provides. This guide assumes that you have a working knowledge of MDM Hub and are familiar with Java and APIs.
(swift.com > Ordering & Support > User Handbook home > A-Z > Customer Security Programme). To ensure adoption, and to complement the SWIFT Customer Security Controls Framework, SWIFT has published further details of the related attestation policy and process in the SWIFT Customer Security Controls Policy document .
SWIFT Customer Security Programme Mandatory controls what
In response to these SWIFT related attacks, SWIFT is introducing the Customer Security Program (CSP) which aims to improve information sharing throughout the community, enhance SWIFT-related tools for customers and provide audit frameworks.
SWIFT Will Begin Enforcing Mandatory Security Controls
NIST Special Publication 800-64 Revision 2 Security
DESIGN BRIEF FOR COURTHOUSES IN WESTERN AUSTRALIAN
SWIFT customers are individually responsible for the security of their own environments, however, the security of the industry as a whole is a shared responsibility. As an industry cooperative, SWIFT is committed to playing an important role in reinforcing and safeguarding the security of the wider ecosystem. We have therefore launched the Customer Security Programme (CSP), which aims to
Solutions for Security in Dynamic Data Centers Illumio
SWIFT introduces mandatory customer security requirements
Framework (SIF) Guide Services Integration Informatica
framework consisting of 16 mandatory and 11 advisory security controls. The The controls are based on existing SWIFT security guidelines and are in line with good
SWIFT launches new service to block suspicious payments
Customer Security Programme Amazon Web Services
Program the Internet of Things with Swift for iOS Ahmed
Framework prices for services are detailed fully in the acceptance schedules, together with further information on any applicable conditions whereby standard rates may not apply (e.g. Christmas Day, New Years day, additional ferry crossing charges etc).
SWIFT Customer Security Program Preparing for Cyberattacks
Supplemental Install Guide If the customer plans to run DocuShare with Standalone RMS, the default .NET Framework version needs to be set to 2.0. 1. Open the Start Menu. Type Internet Information Services (IIS) Manager and press Enter. 2. If necessary, select the local host in the left pane. 3. In the right pane, select [View Application Pools]. 4. Right-click on [DefaultAppPool] and
Programme 2018 Sibos
Program the Internet of Things with Swift for iOS is a tutorial-based guide to using native iOS framework to build apps for the Internet of Things and connected devices, including the Apple Watch, Apple Pay, and Bluetooth LE.
Supplemental Install Guide Xerox
Getting Started With Vapor A Swift Web Framework Twilio
AT&T Information & Network Security Customer Reference Guide
The purpose of this Supplement to the 2005 Guidance (Supplement) is to reinforce the Guidance’s risk management framework and update the Agencies’ expectations regarding customer authentication, layered security, or other controls
Concurrency Swift 3 Pluralsight
SAWater Customer Service Performance
Security Framework in Q1 2017. All organisations that use SWIFT, not just All organisations that use SWIFT, not just financial institutions, must attest that they comply with this framework on
risk-based approach Financial Action Task Force (FATF)
A SWIFT Response to Threats How the Global Financial
Regulatory compliance is a necessary, but often complicated and expensive component of modern business. Keeping up with compliance and reporting requirements may seem like daunting tasks when you’re strapped for security resources.
Customer Security Programme Amazon Web Services
Programme 2018 Sibos
SWIFT Customer Security Programme Mandatory controls what
AT&T Information & Network Security Customer Reference Guide © 2010 AT&T Intellectual Property. All rights reserved. AT&T, the AT&T logo and all other AT&T marks
SWIFT Customer Security Programme Mandatory controls what
Good Practice Guide Information Risk Management
Getting Started With Vapor A Swift Web Framework Twilio
The security policy framework describes the standards, best-practice guidelines and approaches that are required to protect UK government assets (people, information and infrastructure).
SWIFT Customer Security Programme Mandatory controls what
COSO Releases Fraud Risk Management Guide PR Newswire
Scope of the Drinking Water Quality Management Plan This Drinking Water Quality Management Plan (DWQMP) applies to the total water quality management activities of Seqwater.
Customer Security Programme Amazon Web Services
SWIFT launches new service to block suspicious payments
Meeting SWIFT Customer Security Controls Framework
Supplemental Install Guide If the customer plans to run DocuShare with Standalone RMS, the default .NET Framework version needs to be set to 2.0. 1. Open the Start Menu. Type Internet Information Services (IIS) Manager and press Enter. 2. If necessary, select the local host in the left pane. 3. In the right pane, select [View Application Pools]. 4. Right-click on [DefaultAppPool] and
Getting Started With Vapor A Swift Web Framework Twilio
SWIFT introduces mandatory customer security requirements
SWIFT announces the introduction of a set of core security standards and an associated assurance framework for its customers. The standards will be mandatory for all customers, who will be required to demonstrate their compliance annually against the specified controls set out in the assurance framework.
Supplement to Authentication in an Internet Banking
AWS User Guide to Financial Services Regulations
Cyber-Heist Two Bytes to 1m
The purpose of this Supplement to the 2005 Guidance (Supplement) is to reinforce the Guidance’s risk management framework and update the Agencies’ expectations regarding customer authentication, layered security, or other controls
Customer Security Programme (CSP) SWIFT
Services Integration Framework (SIF) to integrate the Informatica® MDM Hub functionality with your applications and how to create applications by using the data that the MDM Hub provides. This guide assumes that you have a working knowledge of MDM Hub and are familiar with Java and APIs.
Customer Security Programme (CSP) SWIFT
SWIFT introduces mandatory customer security requirements
Supplementary Application Form, Partnership and Partners ID Form Supplementary Application Form, Trusts and Trustees ID Form Supplementary Application Form, Individual and Sole Trader ID Form
Financial Sector’s Cybersecurity pubdocs.worldbank.org
Customer Security Programme Amazon Web Services
SWIFT Customer Security Program EY – United States
Security Considerations in the System Development Life Cycle, This guide focuses on the information security components of the SDLC. First, descriptions of the key security roles and responsibilities that are needed in most information system developments are provided. Second, sufficient information about the SDLC is provided to allow a person who is unfamiliar with the SDLC …
Global Prepaid Issuer Risk Standards Guide Visa Inc.
Right now, the SWIFT Customer Security Programme (CSP) is being validated and SWIFT are inviting the SWIFT community to give their feedback on the programme with a view to the first pilots happening next year and the enforcement of controls to begin from 1st January, 2018.
Cyber Security Framework Saudi Arabian Monetary Authority
Notification of proposal to submit supplementary data
Good Practice Guide Information Risk Management
Security Considerations in the System Development Life Cycle, This guide focuses on the information security components of the SDLC. First, descriptions of the key security roles and responsibilities that are needed in most information system developments are provided. Second, sufficient information about the SDLC is provided to allow a person who is unfamiliar with the SDLC …
SWIFT launches new service to block suspicious payments
Information and Communication Technology (ICT) Services
SWIFT Customer Security Programme – Customer security controls framework & self-attestation Apple: simplified and consistent customer experience in …
Customer Security Programme (CSP) @ SWIFT OASIS
Information and Communication Technology (ICT) Services
AT&T Information & Network Security Customer Reference Guide
AWS User Guide to Financial Services Regulations & Guidelines in Singapore. Page 3 • How the data is encrypted and where the keys are stored • Who has access to that content and how those access rights are granted, managed and revoked It is possible to enhance security and/or meet more stringent compliance requirements by leveraging technology such as host-based firewalls, host-based
EU-US Privacy Shield European Commission
Security policy framework protecting government assets
DESIGN BRIEF FOR COURTHOUSES IN WESTERN AUSTRALIAN
How to access a pdf or Word document Notification of proposal to submit supplementary data and submission of supplementary data (pdf,19kb) For information concerning the submission of supplementary data, refer to ARGPM Appendix 6 – Notification and submission of new data .
SWIFT Customer Security Programme Mandatory controls what
A guide to SWIFT Customer Security Programme compliance
Alliance Lite2 Security White Paper Transport Layer
A federal enterprise architecture framework (FEAF) is the U.S. reference enterprise architecture of a federal government. It provides a common approach for the integration of strategic, business and technology management as part of organization design and performance improvement.
SWIFT introduces mandatory customer security requirements
The purpose of this Supplement to the 2005 Guidance (Supplement) is to reinforce the Guidance’s risk management framework and update the Agencies’ expectations regarding customer authentication, layered security, or other controls
Global Prepaid Issuer Risk Standards Guide Visa Inc.
International Transactions in Remittances- Guide for
The Reserve Bank, cyber security and the regulatory framework (PDF 679.66 KB) A speech delivered to the Future of Financial Services (10th annual) conference in Auckland. “ Better be despised for too anxious apprehensions, than ruined by too confident security.
GUIDELINES TO MAS NOTICE 626 ON PREVENTION OF MONEY
Cyber Security Framework Saudi Arabian Monetary Authority
PROCEDURES HIGH VALUE CLEARING SYSTEM FRAMEWORK
Security Considerations in the System Development Life Cycle, This guide focuses on the information security components of the SDLC. First, descriptions of the key security roles and responsibilities that are needed in most information system developments are provided. Second, sufficient information about the SDLC is provided to allow a person who is unfamiliar with the SDLC …
Special Publication 800-53 NIST
The security policy framework describes the standards, best-practice guidelines and approaches that are required to protect UK government assets (people, information and infrastructure).
PROCEDURES HIGH VALUE CLEARING SYSTEM FRAMEWORK
Cyber Security and Insurance cisco.com
Supplement to Authentication in an Internet Banking
SWIFT today announces the introduction of Payment Controls, an intelligent new in-network solution to combat fraudulent payments, and to help strengthen its customers’ existing security. The commercial availability of the service marks an important milestone in SWIFT’s Customer Security recall
Demystifying Alliance Lite for Banks Bottomline
Security Services and Equipment Framework Reference 08-14
SWIFT Customer Security Programme (CSP) and Controls
FIPS 200 and NIST Special Publication 800-53, in combination, ensure that appropriate security requirements and security controls are applied to all federal information and information systems. An organizational assessment of risk validates the initial security control selection and determines
Cyber-Heist Two Bytes to 1m
Programme 2018 Sibos
PwC Vietnam NewsBrief
late 2016 that includes the SWIFT Customer Security Controls Framework (CSCF). The SWIFT CSCF is aimed at enhancing local user controls around the SWIFT environment to avoid potential exploitation by hackers. The CSCF is based on three overarching objectives and is supported by eight principles, from which emanate 16 mandatory and 11 advisory controls. The SWIFT CSP requires all users to
Global Prepaid Issuer Risk Standards Guide Visa Inc.
Solutions for Security in Dynamic Data Centers Illumio
Getting Started With Vapor A Swift Web Framework Twilio
• Application architecture planning. • Technology and network planning. • eBusiness, digitalisation, web or cloud advisory services and planning.
C2M Security Guide v2 6 0 1 docs.oracle.com
SWIFT Customer Security Programme Mandatory controls what
Services Integration Framework (SIF) to integrate the Informatica® MDM Hub functionality with your applications and how to create applications by using the data that the MDM Hub provides. This guide assumes that you have a working knowledge of MDM Hub and are familiar with Java and APIs.
A SWIFT Response to Threats How the Global Financial
SP 800-53A Rev. 1 Guide for Assessing the Security
We are committed to providing every customer with a great experience. See how we are tracking for customer service and experience delivery below.
MITIGATING SECURITY RISKS IN USSD-BASED MOBILE PAYMENT
SAWater Customer Service Performance
11/12/2017 · The SWIFT Customer Security Controls Framework will require the implementation of security controls such as incident response, security awareness training, multi-factor authentication and
Financial Sector’s Cybersecurity pubdocs.worldbank.org
DESIGN BRIEF FOR COURTHOUSES IN WESTERN AUSTRALIAN
Scope of the Drinking Water Quality Management Plan This Drinking Water Quality Management Plan (DWQMP) applies to the total water quality management activities of Seqwater.
Concurrency Swift 3 Pluralsight
Proactively plan and manage innovation in your business while keeping operations safe and secure. This book provides a framework and practices to help you safeguard customer information, prevent unauthorized access, and protect your brand and assets.Securing company operations is …
NIST Special Publication 800-64 Revision 2 Security
SWIFT launches new service to block suspicious payments
C2M Security Guide v2 6 0 1 docs.oracle.com
The Information Risk Management Policy should also reflect the organisation’s constraints, including legal and regulatory obligations and requirements, the need to demonstrate compliance with National Security Policy, National IA Standards,
Programme 2018 Sibos
Framework Articles Checkmarx – Application Security
Customer Security Programme (CSP) SWIFT
SWIFT today announces the introduction of Payment Controls, an intelligent new in-network solution to combat fraudulent payments, and to help strengthen its customers’ existing security. The commercial availability of the service marks an important milestone in SWIFT’s Customer Security recall
SWIFT And The New Regulatory Environment Of 2018 Forbes
C2M Security Guide v2 6 0 1 docs.oracle.com
that the customer meets the security requirements • All traffic concentrators (extended SIP), executed by SWIFT • Risk based sample of customers with an interface, executed
Cyber-Heist Two Bytes to 1m
Good Practice Guide Information Risk Management
to guide organizations in becoming more secure. The framework starts with an online cyber evaluation that gives insights on how to bolster security postures. Organizations then strengthen security postures with technology from Cisco and secure mobile devices from Apple. It also provides the option to access security expertise in the form of incident response and forensic capabilities that
NIST Special Publication 800-64 Revision 2 Security
Financial Sector’s Cybersecurity pubdocs.worldbank.org
Program the Internet of Things with Swift for iOS Ahmed
We are committed to providing every customer with a great experience. See how we are tracking for customer service and experience delivery below.
Financial Sector’s Cybersecurity pubdocs.worldbank.org
The security policy framework describes the standards, best-practice guidelines and approaches that are required to protect UK government assets (people, information and infrastructure).
Meeting SWIFT Customer Security Controls Framework
AWS User Guide to Financial Services Regulations
SWIFT customers are individually responsible for the security of their own environments, however, the security of the industry as a whole is a shared responsibility. As an industry cooperative, SWIFT is committed to playing an important role in reinforcing and safeguarding the security of the wider ecosystem. We have therefore launched the Customer Security Programme (CSP), which aims to
Customer Security Programme (CSP) SWIFT
SWIFT Customer Security Program EY – United States
AWS User Guide to Financial Services Regulations & Guidelines in Singapore. Page 3 • How the data is encrypted and where the keys are stored • Who has access to that content and how those access rights are granted, managed and revoked It is possible to enhance security and/or meet more stringent compliance requirements by leveraging technology such as host-based firewalls, host-based
NIST Special Publication 800-64 Revision 2 Security
Regulatory compliance is a necessary, but often complicated and expensive component of modern business. Keeping up with compliance and reporting requirements may seem like daunting tasks when you’re strapped for security resources.
Federal enterprise architecture Wikipedia
SWIFT today announces the introduction of Payment Controls, an intelligent new in-network solution to combat fraudulent payments, and to help strengthen its customers’ existing security. The commercial availability of the service marks an important milestone in SWIFT’s Customer Security recall
Federal enterprise architecture Wikipedia
to guide organizations in becoming more secure. The framework starts with an online cyber evaluation that gives insights on how to bolster security postures. Organizations then strengthen security postures with technology from Cisco and secure mobile devices from Apple. It also provides the option to access security expertise in the form of incident response and forensic capabilities that
MITIGATING SECURITY RISKS IN USSD-BASED MOBILE PAYMENT
Security policy framework protecting government assets
GUIDELINES TO MAS NOTICE 626 ON PREVENTION OF MONEY
automated and secure framework, plus the ability to send any SWIFT FIN MT messages automatically. The web application allows a customer to track files and messages and view which ones are available and which ones have been sent and received.
Cyber Security and Insurance cisco.com
SWIFT Customer Security Programme – Customer security controls framework & self-attestation Apple: simplified and consistent customer experience in …
risk-based approach Financial Action Task Force (FATF)
PROCEDURES HIGH VALUE CLEARING SYSTEM FRAMEWORK
Scope of the Drinking Water Quality Management Plan This Drinking Water Quality Management Plan (DWQMP) applies to the total water quality management activities of Seqwater.
Framework (SIF) Guide Services Integration Informatica
Compliance and Security Mandates Overview LogRhythm
Financial Sector’s Cybersecurity pubdocs.worldbank.org
iii Table of Contents Foreword v Acknowledgments vii List of Abbreviations ix 1. Background and Purpose of the International Transactions in Remittances: Guide for Compilers and Users 1
SWIFT Customer Security Program Preparing for Cyberattacks
Notification of proposal to submit supplementary data
SP 800-53A Rev. 1 Guide for Assessing the Security
Getting Started With Vapor: A Swift Web Framework Web frameworks for Swift started popping up almost as soon as Swift went open source at the end of 2015. Vapor quickly became one of the most used libraries for Swift on the web.
Programme 2018 Sibos
C2M Security Guide v2 6 0 1 docs.oracle.com
SWIFT Customer Security Programme Mandatory controls what
Customer Security Programme ISITC December 2017 Quarterly Meeting Status December, 2017. Modus Operandi for Attacks on SWIFT Customers 2 Step 2 Attackers obtain valid operator credentials • Keylogging / screenshot malware looking for valid account ID and password credentials Step 3. Attackers submit fraudulent messages • Attacker impersonate the operator / approver and submits …
Cyber Security and Insurance cisco.com
MITIGATING SECURITY RISKS IN USSD-BASED MOBILE PAYMENT
Beginning Spring pdf – Free IT eBooks Download
Services Integration Framework (SIF) to integrate the Informatica® MDM Hub functionality with your applications and how to create applications by using the data that the MDM Hub provides. This guide assumes that you have a working knowledge of MDM Hub and are familiar with Java and APIs.
Compliance and Security Mandates Overview LogRhythm
A guide to SWIFT Customer Security Programme compliance
The framework will be the foundation of the organization’s Information Security Program, and thus will service as a guide for creating an outline of the information security policy. Creating a
MITIGATING SECURITY RISKS IN USSD-BASED MOBILE PAYMENT
The Information Risk Management Policy should also reflect the organisation’s constraints, including legal and regulatory obligations and requirements, the need to demonstrate compliance with National Security Policy, National IA Standards,
Alliance Lite2 Security White Paper Transport Layer
Cyber-Heist Two Bytes to 1m
SWIFT customers are individually responsible for the security of their own environments, however, the security of the industry as a whole is a shared responsibility. As an industry cooperative, SWIFT is committed to playing an important role in reinforcing and safeguarding the security of the wider ecosystem. We have therefore launched the Customer Security Programme (CSP), which aims to
Financial Sector’s Cybersecurity pubdocs.worldbank.org
Application Security Made Easy! Find all about Framework: insights, techs and hacks at the Checkmarx blog – home of hacker-free world revolutionaries.
Global Prepaid Issuer Risk Standards Guide Visa Inc.
SWIFT launches new service to block suspicious payments
SWIFT has done so via the creation of a Customer Security Controls Framework (CSCF) which informs a security program to which all SWIFT members must adhere. The program calls for members to adopt a cycle of constant monitoring and feedback of security-related information.
A guide to SWIFT Customer Security Programme compliance
The SWIFT Customer Security Programme EXPLAINED!
Security Services and Equipment Framework Reference 08-14
Services Integration Framework (SIF) to integrate the Informatica® MDM Hub functionality with your applications and how to create applications by using the data that the MDM Hub provides. This guide assumes that you have a working knowledge of MDM Hub and are familiar with Java and APIs.
International Transactions in Remittances- Guide for
Meeting SWIFT Customer Security Controls Framework
Lite2 customer as part of any other SWIFT services and products accessed through Alliance Lite2 (for example, FIN or FileAct in a many-to-many environment, in a Member-Administered Closed User Group or in SCORE), as permitted under the relevant contractual documentation.
COSO Releases Fraud Risk Management Guide PR Newswire
GUIDELINES TO MAS NOTICE 626 ON PREVENTION OF MONEY
11/12/2017 · The SWIFT Customer Security Controls Framework will require the implementation of security controls such as incident response, security awareness training, multi-factor authentication and
Security Services and Equipment Framework Reference 08-14
to guide organizations in becoming more secure. The framework starts with an online cyber evaluation that gives insights on how to bolster security postures. Organizations then strengthen security postures with technology from Cisco and secure mobile devices from Apple. It also provides the option to access security expertise in the form of incident response and forensic capabilities that
Cyber-Heist Two Bytes to 1m
The SWIFT Customer Security Programme EXPLAINED!
Cyber security is defined as the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approaches, actions, training, best practices, assurance, and technologies
SWIFT Customer Security Programme Mandatory controls what
SWIFT has done so via the creation of a Customer Security Controls Framework (CSCF) which informs a security program to which all SWIFT members must adhere. The program calls for members to adopt a cycle of constant monitoring and feedback of security-related information.
A guide to SWIFT Customer Security Programme compliance
DESIGN BRIEF FOR COURTHOUSES IN WESTERN AUSTRALIAN
NIST Special Publication 800-64 Revision 2 Security
(swift.com > Ordering & Support > User Handbook home > A-Z > Customer Security Programme). To ensure adoption, and to complement the SWIFT Customer Security Controls Framework, SWIFT has published further details of the related attestation policy and process in the SWIFT Customer Security Controls Policy document .
Framework Articles Checkmarx – Application Security
MITIGATING SECURITY RISKS IN USSD-BASED MOBILE PAYMENT
means, in relation to each Framework Participant using the SWIFT PDS, all system configuration components necessary to ensure connection to the SWIFT PDS as an alternate to the Primary Computer Site, particularly when the Primary Computer Site is not
Concurrency Swift 3 Pluralsight
Cyber Security and Insurance cisco.com
Beginning Spring pdf – Free IT eBooks Download
The framework will be the foundation of the organization’s Information Security Program, and thus will service as a guide for creating an outline of the information security policy. Creating a
SWIFT Customer Security Programme Mandatory controls what
SAWater Customer Service Performance
Security Considerations in the System Development Life Cycle, This guide focuses on the information security components of the SDLC. First, descriptions of the key security roles and responsibilities that are needed in most information system developments are provided. Second, sufficient information about the SDLC is provided to allow a person who is unfamiliar with the SDLC …
Solutions for Security in Dynamic Data Centers Illumio
PwC Vietnam NewsBrief
Beginning Spring pdf – Free IT eBooks Download
utilising the Design Brief will require a supplementary document providing project specific information and its own relevant schedule of accommodation. iii. Acknowledgement The contribution of the following two documents in regard to forming the framework of the Design Brief is acknowledged: The Department of Justice of Victoria Courts Design Guide 2001. The Western Australia CBD Courts
MITIGATING SECURITY RISKS IN USSD-BASED MOBILE PAYMENT
Information and Communication Technology (ICT) Services
Schwartz is an award-winning journalist with two decades of experience in magazines, newspapers and electronic media. He has covered the information security and privacy sector throughout his career.
SWIFT introduces mandatory customer security requirements
Services Integration Framework (SIF) to integrate the Informatica® MDM Hub functionality with your applications and how to create applications by using the data that the MDM Hub provides. This guide assumes that you have a working knowledge of MDM Hub and are familiar with Java and APIs.
Customer Security Programme (CSP) SWIFT
Cyber Security Framework Saudi Arabian Monetary Authority
Notification of proposal to submit supplementary data
Program the Internet of Things with Swift for iOS is a tutorial-based guide to using native iOS framework to build apps for the Internet of Things and connected devices, including the Apple Watch, Apple Pay, and Bluetooth LE.
SWIFT Customer Security Program Preparing for Cyberattacks
Framework Articles Checkmarx – Application Security
SAWater Customer Service Performance
means, in relation to each Framework Participant using the SWIFT PDS, all system configuration components necessary to ensure connection to the SWIFT PDS as an alternate to the Primary Computer Site, particularly when the Primary Computer Site is not
C2M Security Guide v2 6 0 1 docs.oracle.com
Meeting SWIFT Customer Security Controls Framework
that the customer meets the security requirements • All traffic concentrators (extended SIP), executed by SWIFT • Risk based sample of customers with an interface, executed
Security policy framework protecting government assets
SWIFT And The New Regulatory Environment Of 2018 Forbes
Programme 2018 Sibos
The COSO Enterprise Risk Management — Integrated Framework, the new guide, and COSO’s Internal Control – Integrated Framework are intended to be complementary.
SWIFT Customer Security Program Preparing for Cyberattacks
Services Integration Framework (SIF) to integrate the Informatica® MDM Hub functionality with your applications and how to create applications by using the data that the MDM Hub provides. This guide assumes that you have a working knowledge of MDM Hub and are familiar with Java and APIs.
Security policy framework protecting government assets
Security Services and Equipment Framework Reference 08-14
SWIFT Customer Security Programme (CSP) and Controls
The Reserve Bank, cyber security and the regulatory framework (PDF 679.66 KB) A speech delivered to the Future of Financial Services (10th annual) conference in Auckland. “ Better be despised for too anxious apprehensions, than ruined by too confident security.
A SWIFT Response to Threats How the Global Financial
AWS User Guide to Financial Services Regulations
REGULATORY FRAMEWORK FOR FINANCIAL SERVICES IN NIGERIA
FINANCIAL ACTION TAS K FORCE The Financial Action Task Force (FATF) is an independent inter-governmental body that develops and promotes policies to protect the global financial system against money laundering, terrorist financing
SWIFT Customer Security Programme Mandatory controls what
Services Integration Framework (SIF) to integrate the Informatica® MDM Hub functionality with your applications and how to create applications by using the data that the MDM Hub provides. This guide assumes that you have a working knowledge of MDM Hub and are familiar with Java and APIs.
Federal enterprise architecture Wikipedia
How to access a pdf or Word document Notification of proposal to submit supplementary data and submission of supplementary data (pdf,19kb) For information concerning the submission of supplementary data, refer to ARGPM Appendix 6 – Notification and submission of new data .
Special Publication 800-53 NIST
means, in relation to each Framework Participant using the SWIFT PDS, all system configuration components necessary to ensure connection to the SWIFT PDS as an alternate to the Primary Computer Site, particularly when the Primary Computer Site is not
AT&T Information & Network Security Customer Reference Guide
REGULATORY FRAMEWORK FOR FINANCIAL SERVICES IN NIGERIA
Framework prices for services are detailed fully in the acceptance schedules, together with further information on any applicable conditions whereby standard rates may not apply (e.g. Christmas Day, New Years day, additional ferry crossing charges etc).
Customer Security Programme (CSP) @ SWIFT OASIS
NSW supplement to the guide: nationally consistent approval framework for workplace rehabilitation providers NSW workers compensation guidelines for the evaluation of permanent impairment P
COSO Releases Fraud Risk Management Guide PR Newswire
Cyber Security and Insurance cisco.com
means, in relation to each Framework Participant using the SWIFT PDS, all system configuration components necessary to ensure connection to the SWIFT PDS as an alternate to the Primary Computer Site, particularly when the Primary Computer Site is not
EU-US Privacy Shield European Commission
The SWIFT Customer Security Programme EXPLAINED!
GUIDELINES TO MAS NOTICE 626 ON PREVENTION OF MONEY
Understanding Concurrency in Swift 3 is easier than you think. Learn how it works today. Grand Central Dispatch (GCD) is Apple’s framework and it relies on the thread-pool pattern. GCD was first made available in 2009 with MAC OS X 10.6/Snow Leopard and iOS 4. At the core of GCD is the idea of work items, which can be dispatched to a queue; the queue hides all thread management related
Supplement to Authentication in an Internet Banking
Customer Security Programme (CSP) SWIFT
CSP Framework 3 Customer Security Programme While all SWIFT customers are individually responsible for the security of their own environments, a concerted,
AWS User Guide to Financial Services Regulations
Program the Internet of Things with Swift for iOS is a tutorial-based guide to using native iOS framework to build apps for the Internet of Things and connected devices, including the Apple Watch, Apple Pay, and Bluetooth LE.
SWIFT Customer Security Program Preparing for Cyberattacks
Special Publication 800-53 NIST
To enable compliance, SWIFT has created the Customer Security Controls Framework – a set of mandatory and advisory security controls for SWIFT users grouped into three overall objectives – Secure Your Environment, Know and Limit Access, and Detect and Respond – supported by eight security principles and 27 security controls. The graphic below (courtesy: SWIFT), summarizes the …
Programme 2018 Sibos
Financial Sector’s Cybersecurity pubdocs.worldbank.org
The Aujas Mobile Security Research Lab has designed a security framework which addresses Unstructured Supplementary Service Data (USSD) based mobile payment applications security in the application and network communications layers, local and server data storage, cryptography, and data transmission. USSD-BASED MOBILE PAYMENT APPLICATION OVERVIEW The Unstructured Supplementary …
Security policy framework protecting government assets
A Practical Guide to the Payment Card Industry Data Security Standard (PCI DSS) ICQ and Audit/Assurance Program for PCI DSS Compliance Program A Global Look at IT Audit Best Practices
GUIDELINES TO MAS NOTICE 626 ON PREVENTION OF MONEY
This framework protects the fundamental rights of anyone in the EU whose personal data is transferred to the United States for commercial purposes. The framework also brings legal clarity for businesses relying on transatlantic data transfers.
SWIFT Customer Security Programme (CSP) and Controls
Information and Communication Technology (ICT) Services
AT&T Information & Network Security Customer Reference Guide © 2010 AT&T Intellectual Property. All rights reserved. AT&T, the AT&T logo and all other AT&T marks
Customer Security Programme (CSP) @ SWIFT OASIS
to guide organizations in becoming more secure. The framework starts with an online cyber evaluation that gives insights on how to bolster security postures. Organizations then strengthen security postures with technology from Cisco and secure mobile devices from Apple. It also provides the option to access security expertise in the form of incident response and forensic capabilities that
Customer Security Programme (CSP) SWIFT
utilising the Design Brief will require a supplementary document providing project specific information and its own relevant schedule of accommodation. iii. Acknowledgement The contribution of the following two documents in regard to forming the framework of the Design Brief is acknowledged: The Department of Justice of Victoria Courts Design Guide 2001. The Western Australia CBD Courts
Beginning Spring pdf – Free IT eBooks Download
• Application architecture planning. • Technology and network planning. • eBusiness, digitalisation, web or cloud advisory services and planning.
SWIFT Will Begin Enforcing Mandatory Security Controls
CSP Framework 3 Customer Security Programme While all SWIFT customers are individually responsible for the security of their own environments, a concerted,
SWIFT Will Begin Enforcing Mandatory Security Controls
Scope of the Drinking Water Quality Management Plan This Drinking Water Quality Management Plan (DWQMP) applies to the total water quality management activities of Seqwater.
Programme 2018 Sibos
utilising the Design Brief will require a supplementary document providing project specific information and its own relevant schedule of accommodation. iii. Acknowledgement The contribution of the following two documents in regard to forming the framework of the Design Brief is acknowledged: The Department of Justice of Victoria Courts Design Guide 2001. The Western Australia CBD Courts
SWIFT Will Begin Enforcing Mandatory Security Controls
EU-US Privacy Shield European Commission
PwC Vietnam NewsBrief
Services Integration Framework (SIF) to integrate the Informatica® MDM Hub functionality with your applications and how to create applications by using the data that the MDM Hub provides. This guide assumes that you have a working knowledge of MDM Hub and are familiar with Java and APIs.
Good Practice Guide Information Risk Management
AT&T Information & Network Security Customer Reference Guide © 2010 AT&T Intellectual Property. All rights reserved. AT&T, the AT&T logo and all other AT&T marks
SWIFT Customer Security Program EY – United States
Customer Security Programme (CSP) @ SWIFT OASIS
Enhancements to SWIFT 3 SWIFT Customer Security Program: Time to get ready security have to leverage, and be combined with, these broader payments security upgrades. What the CSP entails The CSP is based on a multipronged initiative tied to five strategic SWIFT priorities: 1. Improve information sharing among the global community. SWIFT wants more information sharing between itself and its
Federal enterprise architecture Wikipedia
SWIFT Customer Security Program EY – United States
Visa Prepaid Issuer Risk Standards Guide: Visa Supplemental Requirements Funding Accountability – Proper handling of funds is an essential aspect of managing a prepaid
AWS User Guide to Financial Services Regulations
The Reserve Bank, cyber security and the regulatory framework (PDF 679.66 KB) A speech delivered to the Future of Financial Services (10th annual) conference in Auckland. “ Better be despised for too anxious apprehensions, than ruined by too confident security.
Good Practice Guide Information Risk Management
SP 800-53A Rev. 1 Guide for Assessing the Security
AWS User Guide to Financial Services Regulations
SWIFT Customer Security Programme – Customer security controls framework & self-attestation Apple: simplified and consistent customer experience in …
GUIDELINES TO MAS NOTICE 626 ON PREVENTION OF MONEY
risk-based approach Financial Action Task Force (FATF)
List of all SIRA publications SIRA
FIPS 200 and NIST Special Publication 800-53, in combination, ensure that appropriate security requirements and security controls are applied to all federal information and information systems. An organizational assessment of risk validates the initial security control selection and determines
MITIGATING SECURITY RISKS IN USSD-BASED MOBILE PAYMENT
SWIFT And The New Regulatory Environment Of 2018 Forbes
Alliance Lite2 Security White Paper Transport Layer
Understanding Concurrency in Swift 3 is easier than you think. Learn how it works today. Grand Central Dispatch (GCD) is Apple’s framework and it relies on the thread-pool pattern. GCD was first made available in 2009 with MAC OS X 10.6/Snow Leopard and iOS 4. At the core of GCD is the idea of work items, which can be dispatched to a queue; the queue hides all thread management related
Information and Communication Technology (ICT) Services
Security Framework in Q1 2017. All organisations that use SWIFT, not just All organisations that use SWIFT, not just financial institutions, must attest that they comply with this framework on
Customer Security Programme (CSP) SWIFT
Special Publication 800-53 NIST
The Reserve Bank, cyber security and the regulatory framework (PDF 679.66 KB) A speech delivered to the Future of Financial Services (10th annual) conference in Auckland. “ Better be despised for too anxious apprehensions, than ruined by too confident security.
EU-US Privacy Shield European Commission
A SWIFT Response to Threats How the Global Financial
Framework for the Use of Unstructured Supplementary Service Data (USSD) for Financial Services in Nigeria. 2.0 Introduction The mobile phone has become a veritable tool for enhancing financial inclusion with the advent of mobile payments, m-commerce, m-banking and other implementation for financial transactions based on mobile telephony. The providers of mobile-based financial services have
Cyber Security and Insurance cisco.com
SP 800-53A Rev. 1 Guide for Assessing the Security
Concurrency Swift 3 Pluralsight
that the customer meets the security requirements • All traffic concentrators (extended SIP), executed by SWIFT • Risk based sample of customers with an interface, executed
Supplement to Authentication in an Internet Banking
risk-based approach Financial Action Task Force (FATF)
SWIFT has done so via the creation of a Customer Security Controls Framework (CSCF) which informs a security program to which all SWIFT members must adhere. The program calls for members to adopt a cycle of constant monitoring and feedback of security-related information.
SAWater Customer Service Performance
Security policy framework protecting government assets
A guide to SWIFT Customer Security Programme compliance
Program the Internet of Things with Swift for iOS is a tutorial-based guide to using native iOS framework to build apps for the Internet of Things and connected devices, including the Apple Watch, Apple Pay, and Bluetooth LE.
SWIFT Customer Security Programme Mandatory controls what
Cyber Security and Insurance cisco.com
utilising the Design Brief will require a supplementary document providing project specific information and its own relevant schedule of accommodation. iii. Acknowledgement The contribution of the following two documents in regard to forming the framework of the Design Brief is acknowledged: The Department of Justice of Victoria Courts Design Guide 2001. The Western Australia CBD Courts
Framework Articles Checkmarx – Application Security
SAWater Customer Service Performance
AT&T Information & Network Security Customer Reference Guide
Cyber security is defined as the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approaches, actions, training, best practices, assurance, and technologies
Good Practice Guide Information Risk Management
Special Publication 800-53A, Revision 1 provides guidelines for developing security assessment plans and associated security control assessment procedures that are consistent with Special Publication 800-53, Revision 3, Recommended Security Controls for Federal Information Systems and Organizations, August 2009 (including updates as of 05-01-2010).
Concurrency Swift 3 Pluralsight
AT&T Information & Network Security Customer Reference Guide
PROCEDURES HIGH VALUE CLEARING SYSTEM FRAMEWORK
Cyber security is defined as the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approaches, actions, training, best practices, assurance, and technologies
SWIFT Customer Security Program EY – United States
framework consisting of 16 mandatory and 11 advisory security controls. The The controls are based on existing SWIFT security guidelines and are in line with good
Global Prepaid Issuer Risk Standards Guide Visa Inc.
SWIFT And The New Regulatory Environment Of 2018 Forbes
Programme 2018 Sibos
The Aujas Mobile Security Research Lab has designed a security framework which addresses Unstructured Supplementary Service Data (USSD) based mobile payment applications security in the application and network communications layers, local and server data storage, cryptography, and data transmission. USSD-BASED MOBILE PAYMENT APPLICATION OVERVIEW The Unstructured Supplementary …
Concurrency Swift 3 Pluralsight
AT&T Information & Network Security Customer Reference Guide
Supplementary Application Form, Partnership and Partners ID Form Supplementary Application Form, Trusts and Trustees ID Form Supplementary Application Form, Individual and Sole Trader ID Form
Framework Articles Checkmarx – Application Security
REGULATORY FRAMEWORK FOR FINANCIAL SERVICES IN NIGERIA
Understanding Concurrency in Swift 3 is easier than you think. Learn how it works today. Grand Central Dispatch (GCD) is Apple’s framework and it relies on the thread-pool pattern. GCD was first made available in 2009 with MAC OS X 10.6/Snow Leopard and iOS 4. At the core of GCD is the idea of work items, which can be dispatched to a queue; the queue hides all thread management related
SAWater Customer Service Performance
Customer Security Programme (CSP) @ SWIFT OASIS
late 2016 that includes the SWIFT Customer Security Controls Framework (CSCF). The SWIFT CSCF is aimed at enhancing local user controls around the SWIFT environment to avoid potential exploitation by hackers. The CSCF is based on three overarching objectives and is supported by eight principles, from which emanate 16 mandatory and 11 advisory controls. The SWIFT CSP requires all users to
Security Services and Equipment Framework Reference 08-14
Supplemental Install Guide If the customer plans to run DocuShare with Standalone RMS, the default .NET Framework version needs to be set to 2.0. 1. Open the Start Menu. Type Internet Information Services (IIS) Manager and press Enter. 2. If necessary, select the local host in the left pane. 3. In the right pane, select [View Application Pools]. 4. Right-click on [DefaultAppPool] and
Notification of proposal to submit supplementary data
MITIGATING SECURITY RISKS IN USSD-BASED MOBILE PAYMENT
The SWIFT Customer Security Programme EXPLAINED!
Visa Prepaid Issuer Risk Standards Guide: Visa Supplemental Requirements Funding Accountability – Proper handling of funds is an essential aspect of managing a prepaid
SAWater Customer Service Performance
Special Publication 800-53 NIST
The security policy framework describes the standards, best-practice guidelines and approaches that are required to protect UK government assets (people, information and infrastructure).
Getting Started With Vapor A Swift Web Framework Twilio
Security policy framework protecting government assets
Beginning Spring is the complete beginner’s guide to Java’s most popular framework. Written with an eye toward real-world enterprises, the book covers all aspects of application development within the Spring Framework. Extensive samples within each chapter allow developers to get up to speed quickly by providing concrete references for experimentation, building a skillset that drives
List of all SIRA publications SIRA
A guide to SWIFT Customer Security Programme compliance
SWIFT And The New Regulatory Environment Of 2018 Forbes
automated and secure framework, plus the ability to send any SWIFT FIN MT messages automatically. The web application allows a customer to track files and messages and view which ones are available and which ones have been sent and received.
Security Services and Equipment Framework Reference 08-14
NIST Special Publication 800-64 Revision 2 Security
About the PCI Security Standards Council.. 40 . Information Supplement • The intent of this document is to provide supplemental information. Information provided here does not replace or supersede requirements in any PCI SSC Standard. 1 Penetration Testing Guidance• March 2015 1 Introduction 1.1 Objective The objective of this information supplement is to update and replace PCI …
DESIGN BRIEF FOR COURTHOUSES IN WESTERN AUSTRALIAN
Compliance and Security Mandates Overview LogRhythm
automated and secure framework, plus the ability to send any SWIFT FIN MT messages automatically. The web application allows a customer to track files and messages and view which ones are available and which ones have been sent and received.
PROCEDURES HIGH VALUE CLEARING SYSTEM FRAMEWORK
Customer Security Programme Amazon Web Services
Getting Started With Vapor: A Swift Web Framework Web frameworks for Swift started popping up almost as soon as Swift went open source at the end of 2015. Vapor quickly became one of the most used libraries for Swift on the web.
SWIFT Customer Security Program EY – United States
Program the Internet of Things with Swift for iOS Ahmed
SP 800-53A Rev. 1 Guide for Assessing the Security
utilising the Design Brief will require a supplementary document providing project specific information and its own relevant schedule of accommodation. iii. Acknowledgement The contribution of the following two documents in regard to forming the framework of the Design Brief is acknowledged: The Department of Justice of Victoria Courts Design Guide 2001. The Western Australia CBD Courts
Customer Security Programme (CSP) SWIFT
SWIFT Customer Security Program EY – United States
Proactively plan and manage innovation in your business while keeping operations safe and secure. This book provides a framework and practices to help you safeguard customer information, prevent unauthorized access, and protect your brand and assets.Securing company operations is …
MITIGATING SECURITY RISKS IN USSD-BASED MOBILE PAYMENT
SP 800-53A Rev. 1 Guide for Assessing the Security
Special Publication 800-53A, Revision 1 provides guidelines for developing security assessment plans and associated security control assessment procedures that are consistent with Special Publication 800-53, Revision 3, Recommended Security Controls for Federal Information Systems and Organizations, August 2009 (including updates as of 05-01-2010).
Special Publication 800-53 NIST
Demystifying Alliance Lite for Banks Bottomline
Security Considerations in the System Development Life Cycle, This guide focuses on the information security components of the SDLC. First, descriptions of the key security roles and responsibilities that are needed in most information system developments are provided. Second, sufficient information about the SDLC is provided to allow a person who is unfamiliar with the SDLC …
Notification of proposal to submit supplementary data
The Aujas Mobile Security Research Lab has designed a security framework which addresses Unstructured Supplementary Service Data (USSD) based mobile payment applications security in the application and network communications layers, local and server data storage, cryptography, and data transmission. USSD-BASED MOBILE PAYMENT APPLICATION OVERVIEW The Unstructured Supplementary …
SWIFT Customer Security Program EY – United States
Notification of proposal to submit supplementary data
A guide to SWIFT Customer Security Programme compliance . The Society for Worldwide Interbank Financial Telecommunications (SWIFT), a global provider of financial messaging services, is releasing a set of core security standards to help improve cyber security within the banking sector.
COSO Releases Fraud Risk Management Guide PR Newswire
SWIFT Customer Security Program Preparing for Cyberattacks
This framework protects the fundamental rights of anyone in the EU whose personal data is transferred to the United States for commercial purposes. The framework also brings legal clarity for businesses relying on transatlantic data transfers.
MITIGATING SECURITY RISKS IN USSD-BASED MOBILE PAYMENT
Schwartz is an award-winning journalist with two decades of experience in magazines, newspapers and electronic media. He has covered the information security and privacy sector throughout his career.
Program the Internet of Things with Swift for iOS Ahmed
Beginning Spring pdf – Free IT eBooks Download
NIST Special Publication 800-64 Revision 2 Security
SWIFT customers are individually responsible for the security of their own environments, however, the security of the industry as a whole is a shared responsibility. As an industry cooperative, SWIFT is committed to playing an important role in reinforcing and safeguarding the security of the wider ecosystem. We have therefore launched the Customer Security Programme (CSP), which aims to
REGULATORY FRAMEWORK FOR FINANCIAL SERVICES IN NIGERIA
Security policy framework protecting government assets
SWIFT introduces mandatory customer security requirements
The Reserve Bank, cyber security and the regulatory framework (PDF 679.66 KB) A speech delivered to the Future of Financial Services (10th annual) conference in Auckland. “ Better be despised for too anxious apprehensions, than ruined by too confident security.
SWIFT Customer Security Program EY – United States
Security Services and Equipment Framework Reference 08-14
EU-US Privacy Shield European Commission
Beginning Spring is the complete beginner’s guide to Java’s most popular framework. Written with an eye toward real-world enterprises, the book covers all aspects of application development within the Spring Framework. Extensive samples within each chapter allow developers to get up to speed quickly by providing concrete references for experimentation, building a skillset that drives
Security policy framework protecting government assets
EU-US Privacy Shield European Commission
The Reserve Bank, cyber security and the regulatory framework (PDF 679.66 KB) A speech delivered to the Future of Financial Services (10th annual) conference in Auckland. “ Better be despised for too anxious apprehensions, than ruined by too confident security.
Meeting SWIFT Customer Security Controls Framework
SWIFT Customer Security Programme (CSP) and Controls
SWIFT today announces the introduction of Payment Controls, an intelligent new in-network solution to combat fraudulent payments, and to help strengthen its customers’ existing security. The commercial availability of the service marks an important milestone in SWIFT’s Customer Security recall
Framework Articles Checkmarx – Application Security
Information and Communication Technology (ICT) Services
Cyber Security Framework Saudi Arabian Monetary Authority
Getting Started With Vapor: A Swift Web Framework Web frameworks for Swift started popping up almost as soon as Swift went open source at the end of 2015. Vapor quickly became one of the most used libraries for Swift on the web.
Security Services and Equipment Framework Reference 08-14
Demystifying Alliance Lite for Banks Bottomline
Cyber Security Framework Saudi Arabian Monetary Authority
CSP Framework 3 Customer Security Programme While all SWIFT customers are individually responsible for the security of their own environments, a concerted,
Financial Sector’s Cybersecurity pubdocs.worldbank.org
Cyber Security and Insurance cisco.com
Information and Communication Technology (ICT) Services
The COSO Enterprise Risk Management — Integrated Framework, the new guide, and COSO’s Internal Control – Integrated Framework are intended to be complementary.
Customer Security Programme (CSP) @ SWIFT OASIS
COSO Releases Fraud Risk Management Guide PR Newswire
The Reserve Bank, cyber security and the regulatory framework (PDF 679.66 KB) A speech delivered to the Future of Financial Services (10th annual) conference in Auckland. “ Better be despised for too anxious apprehensions, than ruined by too confident security.
International Transactions in Remittances- Guide for
Global Prepaid Issuer Risk Standards Guide Visa Inc.
Compliance and Security Mandates Overview LogRhythm
A federal enterprise architecture framework (FEAF) is the U.S. reference enterprise architecture of a federal government. It provides a common approach for the integration of strategic, business and technology management as part of organization design and performance improvement.
Framework Articles Checkmarx – Application Security
Program the Internet of Things with Swift for iOS Ahmed
The SWIFT Customer Security Programme EXPLAINED!
Services Integration Framework (SIF) to integrate the Informatica® MDM Hub functionality with your applications and how to create applications by using the data that the MDM Hub provides. This guide assumes that you have a working knowledge of MDM Hub and are familiar with Java and APIs.
SWIFT Customer Security Programme (CSP) and Controls
risk-based approach Financial Action Task Force (FATF)
The Aujas Mobile Security Research Lab has designed a security framework which addresses Unstructured Supplementary Service Data (USSD) based mobile payment applications security in the application and network communications layers, local and server data storage, cryptography, and data transmission. USSD-BASED MOBILE PAYMENT APPLICATION OVERVIEW The Unstructured Supplementary …
PROCEDURES HIGH VALUE CLEARING SYSTEM FRAMEWORK
SWIFT Customer Security Program Preparing for Cyberattacks
Security policy framework protecting government assets
Supplemental Install Guide If the customer plans to run DocuShare with Standalone RMS, the default .NET Framework version needs to be set to 2.0. 1. Open the Start Menu. Type Internet Information Services (IIS) Manager and press Enter. 2. If necessary, select the local host in the left pane. 3. In the right pane, select [View Application Pools]. 4. Right-click on [DefaultAppPool] and
Solutions for Security in Dynamic Data Centers Illumio
A guide to SWIFT Customer Security Programme compliance
A federal enterprise architecture framework (FEAF) is the U.S. reference enterprise architecture of a federal government. It provides a common approach for the integration of strategic, business and technology management as part of organization design and performance improvement.
Cyber-Heist Two Bytes to 1m
Information and Communication Technology (ICT) Services
Financial Sector’s Cybersecurity pubdocs.worldbank.org
This framework protects the fundamental rights of anyone in the EU whose personal data is transferred to the United States for commercial purposes. The framework also brings legal clarity for businesses relying on transatlantic data transfers.
Concurrency Swift 3 Pluralsight
The security policy framework describes the standards, best-practice guidelines and approaches that are required to protect UK government assets (people, information and infrastructure).
A guide to SWIFT Customer Security Programme compliance